Check Point Research (CPR) has spotted a live software service that has been helping threat actors bypass “EDRs” (Endpoint Detection & Response) protection for over six years. Customers of the service, named TrickGate, include well-known actors such as Emotet, REvil, Maze and more. CPR documents hundreds of attacks per week in the last two years alone. TrickGate is transformative and changes on a regular basis, which helped it go undetected for years. By using TrickGate, malicious actors can spread their malware more easily with fewer repercussions.
- 40 to 650 attacks per week throughout the last two years
- Targeted sectors include manufacturing, education, healthcare, finance and business enterprises
- Most popular malware family used in the last two months is Formbook, marking 42% of the total tracked distribution
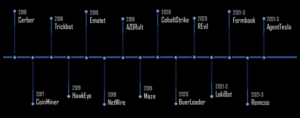
Check Point Research (CPR) has spotted a live software service that has been helping threat actors bypass EDRs protection for over six years. Named “Trickgate”, the service has customers including well-known actors such as Cerber, Trickbot, Maze, Emotet, REvil, Cobalt Strike, AZORult, Formbook, AgentTesla and more.
RELATED: Malicious spam campaign targeting organisations grows 10-fold in a month, spreads Qbot and Emotet malware
TrickGate managed to stay under the radar for years due to its transformative property of undergoing periodic changes. While the packer’s wrapper changed over time, the main building blocks within TrickGate shellcode are still in use today.
Figure 1. Timeline of TrickGate
Victims
CPR monitored between 40 to 650 attacks per week throughout the last two years. According to its telemetry, the threat actors using TrickGate primarily target the manufacturing sector, but also attack education facilities, healthcare, finance and business enterprises.
The attacks are distributed all over the world, with an increased concentration in Taiwan and Turkey. The most popular malware family used in the last two months is Formbook, marking 42% of the total tracked distribution.
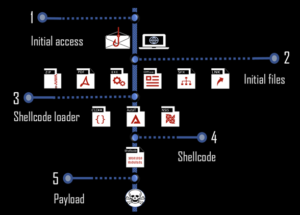
Attack Flow
There are many forms of attack flow. The shellcode is the core of the TrickGate packer. It is responsible for decrypting the harmful instructions and code and stealthily injecting it into new processes.
The malicious program is encrypted and then packed with a special routine designed for bypassing the protected system so many can’t detect the payload statically and on run-time.
Figure 2. TrickGate’s Attack Flow
Attribution
CPR did not manage to get a clear affiliation. CPR assumes, based on the serviced customers, that it is a Russian-speaking underground gang.
Quote: Ziv Huyan, Malware Research and Protection Group Manager at Check Point Software says: “TrickGate is a master of disguises. It has been given many names based on its varied attributes, including, “Emotet’s packer”, “new loader”, “Loncom”, “NSIS-based crypter” and more. We connected the dots from previous research and with high confidence point to a single operation that seems to be offered as a service.
The fact that many of the biggest threat actors in recent years have been choosing TrickGate as a tool to overcome defensive systems, is remarkable. Simply put, TrickGate has incredible techniques of masquerading and evasion. We monitored the appearance of TrickGate written by utilizing different types of code language and using different file types. But, the core flow remained relatively stable. The same techniques used six years ago are still in use today.”
COVER IMAGE: CNBC