In a recent crimeware report, Kaspersky experts have described AdvancedIPSpyware. It is a backdoored version of legitimate Advanced IP Scanner tool used by network admins to control local area networks (LANs). The malicious tool affected a broad audience with victims in Latin America, Africa, Western Europe, South Asia, Australia as well as CIS countries.
RELATED: Kaspersky uncovers spam email campaign targeting businesses worldwide
Adding malicious code to benign software in order to hide its harmful activity and trick the user is a technique that has become increasingly common. What hasn’t been seen as often is that the backdoored binary is actually signed. This is precisely the case of AdvancedIPSpyware, which is a backdoored version of legitimate Advanced IP Scanner tool used by network admins to control LANs.
The certificate with which the malware was signed was most likely stolen. The malware was hosted on two sites, whose domains are almost identical to the legitimate Advanced IP Scanner website, differing only by one the letter. Furthermore, the websites look the same. The only difference is the “free download” button on the malicious websites.
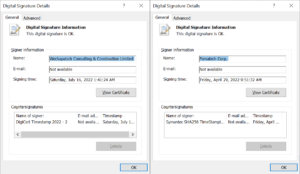
The legitimate signed binary vs the malicious signed binary
Another uncommon feature of AdvancedIPSpyware is that the architecture is modular. Typically, modular architecture is seen with nation-state sponsored malware, not with the criminal type. However, in this case the attacks were not targeted, that drives at the conclusion that AdvancedIPSpyware does not refer to any politically motivated campaigns.
The AdvancedIPSpyware campaign has a broad victimology with affected users in Latin America, Africa, Western Europe, South Asia, Australia as well as CIS countries. The overall count of victims infected over the whole course of the campaign is about 80.
Besides AdvancedIPSpyware, the crimeware report published on Securelist includes the following findings:
- BlackBasta, a ransomware group uncovered earlier in July 2022, added functionality that makes forensics and detection more difficult, as the malware can now propagate through the network itself.
- The researchers witnessed new features of CLoader, a stealer first discovered in April 2022. It used cracked games and software as bait to trick users into installing the malware. The downloaded files were NSIS installers, containing malicious code in the installation script.
- In August 2022, a campaign was discovered that has been active since at least January 2022 and focuses on Chinese-speaking individuals. On a popular Chinese-language YouTube channel, focused on Internet anonymity, a video was uploaded giving instructions on how to install the Tor browser. This itself is not that odd as the Tor browser is blocked in China. However, if a user clicks on the link in the description, instead of the benign Tor browser, an infected version of the Tor browser is downloaded.
“Email is the most common infection method used by both cybercriminals and nation states. This time we took a look at less common techniques employed by cybercriminals – both well-know and that have been stayed out of sight. Namely, the AdvancedIPSpyware stands out for its unusual architecture, usage of legitimate tool, and almost identical copy of the legitimate website,” comments Jornt van der Wiel, a security expert at Kaspersky.
To learn more about AdvancedIPSpyware and other crimeware discoveries, read the report on Securelist.com.
To protect yourself and your business from ransomware attacks, consider following these Kaspersky recommendations:
- Do not expose remote desktop services (such as RDP) to public networks unless absolutely necessary and always use strong passwords for them.
- Promptly install available patches for commercial VPN solutions, providing access for remote employees and acting as gateways in your network.
- Always keep software updated on all the devices you use to prevent ransomware from exploiting vulnerabilities.
- Focus your defense strategy on detecting lateral movements and data exfiltration to the Internet. Pay special attention to outgoing traffic to detect cybercriminals’ connections.
- Back up data regularly. Make sure you can quickly access it in an emergency when needed.
- Use solutions like Kaspersky Endpoint Detection and Response Expert and Kaspersky Managed Detection and Response service, which help identify and stop attacks during the early stages, before attackers reach their final goals.
- Educate your employees to protect the corporate environment. Dedicated training courses can help, such as the ones provided in the Kaspersky Automated Security Awareness Platform.
- Use a reliable endpoint security solution, such as Kaspersky Endpoint Security for Business, that is powered by exploit prevention, behaviour detection and a remediation engine that is able to roll back malicious actions. KESB also has self-defense mechanisms, which can prevent its removal by cybercriminals.
- Use the latest Threat Intelligence information to stay aware of actual TTPs used by threat actors. The Kaspersky Threat Intelligence Portal is a single point of access for Kaspersky’s TI, providing cyberattack data and insights gathered by our team for almost 25 years. To help businesses enable effective defenses in these turbulent times, Kaspersky has announced access to independent, continuously updated and globally sourced information on ongoing cyberattacks and threats, at no charge. Request access to this offer here.